Software Development Company
and Drive Growth through Technology
A Software Development Agency Delivering Software
Excellence for 10 Years
Bespoke software development for web, mobile, and IoT to help you transform, accelerate business performance, and attain efficiency.
Product Engineering
Build and Scale Great Products- Scalable software product development by a proven software developer company that you can depend on
Learn MoreDigital Transformation
Drive Disruption and Transformation using Tech- Crafting digital success stories with software development services that create disruptive products and transform businesses.
Learn MoreBI and Analytics
Unearth Insights to Propel Growth- Helping you deep dive into the data to get insights that drive growth.
Learn MoreCloud Services
Modernize Your Infra- Plan modern cloud infra development, migration, and DevOps implementation services with our software firm.
Learn MoreMobile App Development
Open New Revenue and Customer Service Channels- Build Consumer and Enterprise mobile apps and serve your customers more effectively with our software company.
Learn MoreStaff Augmentation
Scale up or down your software development team on-demand with our software agency’s in-house pool of 200+ developers.
Learn MoreSoftware Agency that’s Crafting Success Stories Since 2010
A proven software development company solving business challenges for top startups and mid-sized businesses
with our expert custom software development services
Auto Accessories Manufacturer Shakes up the Industry with Revolutionary New Business Model
Digital transformation Story of a manufacturer who hired us as their software agency to leveraged technology and build new software applications.
Read the success story
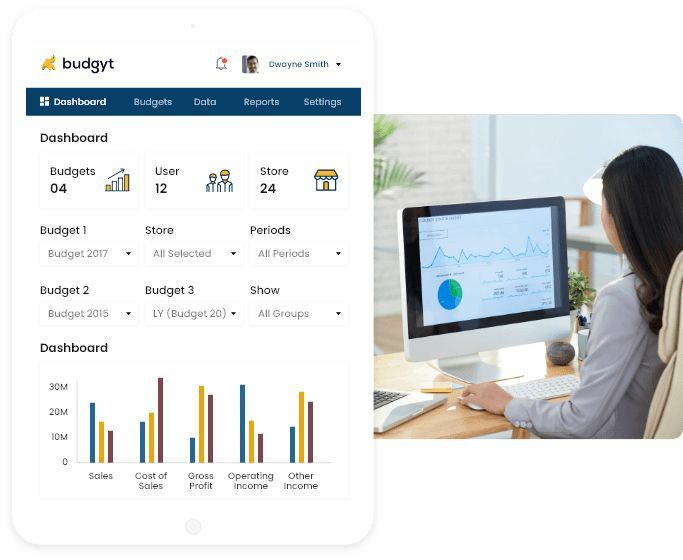
B2B SaaS Company’s Explosive Growth with Forward-thinking Technology Strategies
From MVP to Scaleup, 8+ years of journey as their trusted software development firm.
Read the success storyA Startup’s Triumphant Journey: From PoC to Preferred Airline Union Management App
Engaged us during MVP days as their software development company to build a Pilot Unions Management enterprise app that’s now trusted by top airlines like British airlines, Finnish airlines etc.
Read the success story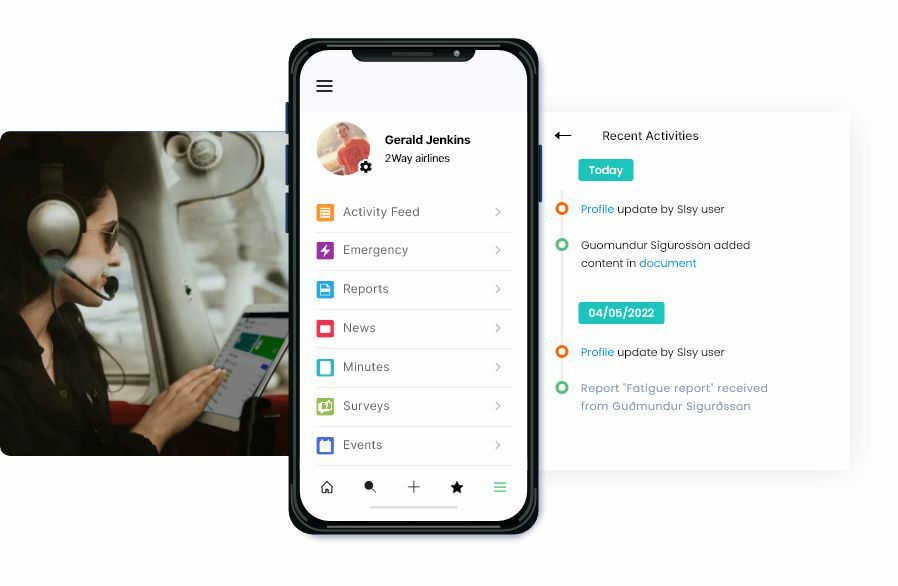
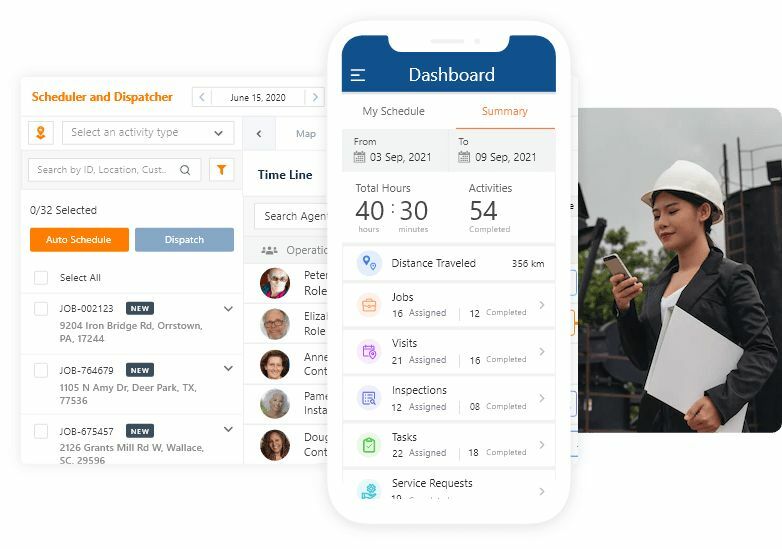
From bootstrapping to Winning Customer Hearts- A B2B SaaS that’s making waves!
A field service software that hired us as their software development firm and is not a scaled-up product.
Trusted by 200+ Businesses as their Software Development Partner
Unlocking value with IT consulting and development services for our customers as their dependable software development firm
A Software Development Agency SMBs and Startup Depend On
Helping startups and SMBs navigate software development challenges as dependable technology partner for their software development services needs.
Reduce Time
Reduce Time to Market-Build Fast, Ship Faster
Transparent & Dependable
Transparent, Dependable, and Certified software company
Reduce Development Costs
Reduce Development Costs without Compromising Quality with our software agency
Build On-demand
Build On-demand with our Experienced & Proven Software Development Agency
A Certified and Accredited Team
Leaders across industries recognize us as a premier software development company for our commitment to quality, professionalism, and strong values.
AWS- Being a standard AWS consulting partner, Finoit’s list of bespoke software development services includes world-class technology solutions for global clients.
Microsoft- As a Microsoft Silver partner software development firm, we deliver high-end software design and development services using various Microsoft technologies
Clutch- Finoit has been featured as a top custom software development company on Clutch, an independent B2B research agency.
ISO 9001- Finoit Technologies is an ISO 9001-certified software development agency for demonstrating the ability to provide software development services in accordance with ISO standards.
ISO 27001- Finoit Technologies received the ISO 27001 certification in information security management for the secure and best development practices we follow as a software development agency.
Nasscom- As one of the fast-growing Nasscom-accredited custom software development firm, we adhere to high-quality, industry best practices for software application development services across various domains.
Our Blog
Our featured blogs share key insights on Software Development, Technologies, Digital Transformation, and the latest industry trends.
+Show blog
Have any of your recent projects failed to achieve your anticipated success? You completed the proje...

Wondering how the words ‘Stealth’ and ‘Business’ can go together? When launching a business,...

As an entrepreneur, to make exit plans from the business that you have put your heart and soul into ...

We all prepare a to-do task list to accomplish our day-to-day tasks. It helps us to retrospect answe...
Get in touch, let’s discuss your project
Risk-free, Trusted Software Development Partner
-
Experienced and Proven
A custom software development firm with over 12 years of credibility in delivering premium software development services.
-
Transparent and Dependable
Micr-level visibility in processes that build trust and makes us a highly transparent software development company.
-
In-budget, On-time
A software development agency that Startups, SMBs, and enterprises rely on for in-budget and on-time delivery of their software development needs.
FAQs
Are you a full-service software agency or just the development?
We are a full-service software agency that covers all aspects of product development i.e. from information flow planning to UX and UI design, software development, testing and software support. We primarily focus on startups and SMBs, and as a software development agency in the US, we understand that being limited to a specific service type would leave our clients overwhelmed as it’s really difficult to get different part of a software development process done from different software development vendors. And for that, as a full-service software company, we ensure that you don’t get stuck or won’t have to hunt other providers because of a lack of software development services mix with us.
How much does software development cost with Finoit?
Project level cost could vary and could be anything between $10,000 to $500,000 or more! That’s what any software design firm would probably also say! Software development cost is affected by various factors such as project requirements, the software development engagement model you choose, and the number of resources/software developers required for your project.
As for hourly rates, could be anything between $15-40/hr depending on technology stack and experience level.
We understand how critical it is to manage the software development cost effectively and for that reason, as a software development firm, we ensure that the planning part is done very meticulously.
Once software development is through, how does your software agency support the software?
As a custom software company, we put great emphasis on uptime and thus software maintenance and support because post-development software support is what helps build a complete and reliable software application. Being a top software development company in USA, we deploy a team of support experts who are at your disposal 24×7. Offering excellent remote technical software support for fixes and issue resolution, our software support staff offers incident-based troubleshooting assistance and provides necessary usability advice as and when you need it.
Are there any specific technologies you prefer/recommend for software development?
Our software development services include a range of technologies and frameworks to build the best-in-class software products. Though we love Python, Java, and native app development, each software development project comes with its own requirements and challenges and we generally recommend software tech stacks accordingly. Of course, as a software developer company, its crtitican that we keep upgrading our tech stacks, and for that reason, we employ modern technology stacks in our services portfolio that helps us cover the broad needs of our customers and makes us the most diversified and the best software development company in USA
What software development methodology do you follow?
This is generally chosen based on budget, timeline, scope definition, etc. As an experienced software development services company, we leverage agile software development methodology to build software applications. However, agile takes various forms such as Scrum, extreme programming (XP), rapid application development (RAD), feature-driven development (FDD), etc. We first analyze the project’s requirements to fit them into a specific agile model. Most of our projects are based on Scrum agile methodology because as a full-service software developer agency, it helps in the quicker release of products to our clients, keeps development costs low, and offers agility to easily incorporate changes in the product.
Are you a custom software development company or also an off-the-shelf software vendor?
We are a custom software development agency in the US and do not offer any off-the-shelf software. We have built our own SaaS and other products but they work separately. As a full-service custom software development firm, we conceptualize and build bespoke software applications from scratch based on our client’s business and process needs. Our full-service custom software development assistance is tailored to meet your unique business needs and goals. For over 13 years now, our software developer company has enabled many startups and small businesses (SMBs) to innovate and add value to their business through our cost-effective custom software development services.
How does your software development company ensure product quality?
With Quality Requirements and Evaluation (SQuaRE). As a known custom software development company in the US(United States), we follow a set of practices to assess quality at each stage in the software development lifecycle. By employing agile methodologies, our software agency builds an iterative pipeline in which software is tested multiple times against the acceptance criteria. And we employ a combination of manual, automated, and semi-automated software testing to test every dimension of the software application.
Amongst so many software development companies, why should we choose you?
Very reasonable questions considering the crowded software product development agency market! Some of the biggest reasons could be:
- We are founders ourselves and know the challenges of building software both as SaaS and internal business processes.
- Trust and dependability in a software development team are critical and that’s what we focus on.
- A partner mindset and not a software agency/vendor mindset is what differentiates us further from the competition.
- Certified software development team, proven credentials, and our reference work and testimonials validate further our capabilities.
Lastly, while optimizing cost is critical, our focus is not on providing low-cost dirt-cheap software development services by compromising on quality like many other development shops. Instead, our goal is to optimize cost while maintaining the highest level of code and software product performance quality. This is what distinguishes us as a software development services company.
As a software development agency, do you hire contractors or have in-house software developers only?
We have a strong team of highly experienced 200+ in-house software developers who are experts in a range of tools and technologies. As a top software developer agency in USA, we believe that bringing external dependency as a software developer company is tricky from accountability, confidentiality, transparency, and many other factors, and for those reasons, we do not hire contractors/freelancers, as we are constantly increasing the size of our in-house software development team. It’s only done if we need a highly experienced consultant for a specific niche in that we do not have the expertise as a trusted software development company.










